How to lock yourself out of your iphone?
Introduction
Imagine a scenario where someone struggles with self-control and cannot effectively manage their screen time. Even with the built-in screen time control features provided by the iPhone, they still find ways to bypass or reset these settings. Consequently, despite the software’s best efforts, it fails to restrict access to the device.
To address this challenge, one potential solution is to use a physical cell phone lock box with a timer. However, this approach requires additional hardware, and its effectiveness may be compromised by the resilience of powerful jailbreaking techniques. Given this context, I am curious whether it would be feasible to design an iPhone locker with a timer that can withstand even the capabilities of post-quantum computers and any potential software-level efforts.
Problem
To design such a locking scheme, a potentially straightforward approach could building upon something from the existing iPhone password system:
If we could somehow change our main password to a new, unknown one without our awareness, we would effectively lock ourselves out of our iPhone!
Discussions
Can we accomplish this entirely on our own? Below is the start of entering password resetting screen:
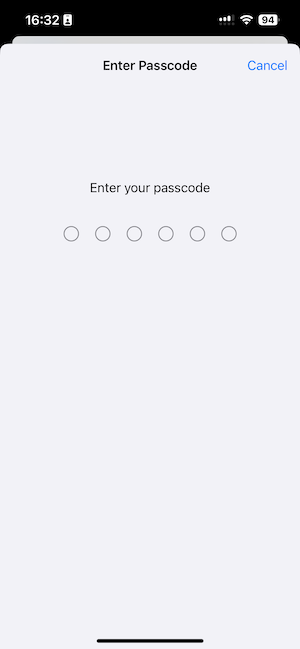
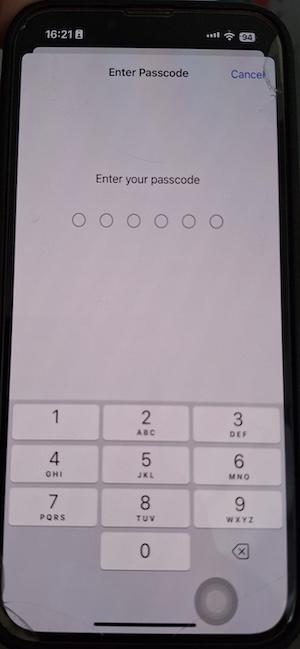
Interestingly, Apple doesn’t allow the digit pad to be screenshoted, as shown clearly with the comparison of two photos above, this might due to Apple’s strict security and privacy protection guideline, in case some external monitoring software recognizing any passowrd related information.
However, as illustrated, the layout of the digits is well-organized and not scrambled. On our own, it is nearly impossible to enter the exact same random 6-digit number without recognizing it. Even if we somehow managed to do so, there is no mechanism in place that provides a timer feature to reveal the altered password after a specified period.
Therefore, we need to rely on a smart assistant that can change the password to a new one without our awareness and subsequently restore it to the original after a user-defined time.
Feasible Direction
To achieve this, our smart assistant should consist of two modules:
- Operational Module: This module will interact with the password management panel and input the new password.
- Software Module: This module must provide at least two features: first, the ability to generate a random passcode without user recognition; second, the capacity to retrieve this passcode only after a specified period.
Operational Module
Purely from a software perspective, it seems Apple blocked any third-party application accessing it’s highly sensitive password management component. Addtionally, password managment is also not shown in the mirrored version of iphone on Mac OS, as verified by testing on iOS 18.5. Conclusively, it seems we have to resort to additional hardware.
Software Module
From a software perspective, we have ample room to innovate in our design. For a 6-digit passcode, there are a total of 1 million possible combinations. While we can easily utilize a Pseudorandom Generator (PRG) to create a random number, the challenge lies in doing so obliviously—essentially generating the number without recognizing or recording it.
If there is only one party involved, achieving this is impossible. However, we could generate the passcode, store it in a time capsule that can only be accessed after a predetermined period, and subsequently retrieve it. There are similar concepts in circulation, such as the Ethereum Unveils Revolutionary On-Chain Time Capsule, but these do not offer precise time control for uncovering the secret, as the time capsule can be opened at any moment prior to the desired time.
Further Application of the Crypto Time Capsule
Consider a scenario where individuals wish to delete sensitive information but still feel a lingering attachment to it. They may prefer to access this information after a delay of 5 or 10 years. In such cases, a crypto time capsule becomes particularly valuable.
Another intriguing application could involve locking sensitive digital assets for a specified duration or creating frozen tokens that remain inaccessible for a defined period. We have all heard anecdotes of individuals forgetting their Bitcoin wallets for years, only to accidentally recover them and discover they are suddenly wealthy. These stories highlight significant use cases that warrant further research into this technology.